Security Audit Pro – Protect Your Store Against AI-Powered Attacks - Module PrestaShop
Security Audit Pro exécute plus de 60 tests d’intrusion sur votre boutique — les mêmes contrôles qu’un auditeur professionnel — et fournit un score de sécurité de A à F avec des instructions de correction exploitables pour chaque vulnérabilité.
8 catégories d’analyse : en-têtes HTTP, fichiers sensibles, sécurité du back-office, base de données CVE des modules, API WebService, injection SQL, XSS/CSRF et contrôle d’accès.
Correction assistée par IA : exportez les résultats dans un fichier structuré, transmettez-le à ChatGPT ou Claude, et laissez l’IA corriger chaque problème.
Chaque résultat inclut ce qui a été détecté, comment corriger étape par étape, ainsi que des détails techniques. Aucune expertise requise. 100 % non intrusif. Compatible PrestaShop 1.7, 8.x & 9.x.
Everything you need, nothing you don't.
The first PrestaShop module that performs a complete security audit with 60+ penetration tests and AI-assisted remediation.
60+ Penetration Tests
Your store is deeply analyzed with the same checks a professional auditor would use, covering all known attack surfaces.
Security Score from A to F
Instantly get a clear overall grade to evaluate your store's protection level and track your improvement over time.
AI-Assisted Remediation
Export results and send them to ChatGPT or Claude to get automatic fixes for every detected vulnerability.
8 Complete Analysis Categories
HTTP headers, sensitive files, back-office, module CVE database, WebService API, SQL injection, XSS/CSRF and access control.
Step-by-Step Instructions, No Expertise Needed
Every result includes what was detected, how to fix it step by step, and the technical details. No security expertise required.
Compatible with PrestaShop 1.7, 8.x & 9.x
One module for all PrestaShop versions. One-click installation, 100% non-intrusive, no changes to your store.
They use it every day.
description Full description expand_more
The First Complete Security Audit & Penetration Testing Module for PrestaShop
With the rise of artificial intelligence, anyone can now find and exploit your store's vulnerabilities in minutes. A single prompt in ChatGPT or Claude is enough to detect exposed configuration files, missing security headers, vulnerable modules, or SQL injection points. What used to require a $3,000+ professional security audit is now available to every attacker — for free.
Security Audit Pro fights back with the same level of intelligence. It performs a complete penetration test of your PrestaShop store — running 60+ automated security checks across 8 categories — directly from your back office, in under 5 minutes. No command line, no server access, no technical skills required.
How It Works — 3 Steps
Step 1 — Scan: Click "Run Full Scan". The module executes 8 independent security scanners sequentially. A real-time progress bar shows which scanner is running and the completion percentage.
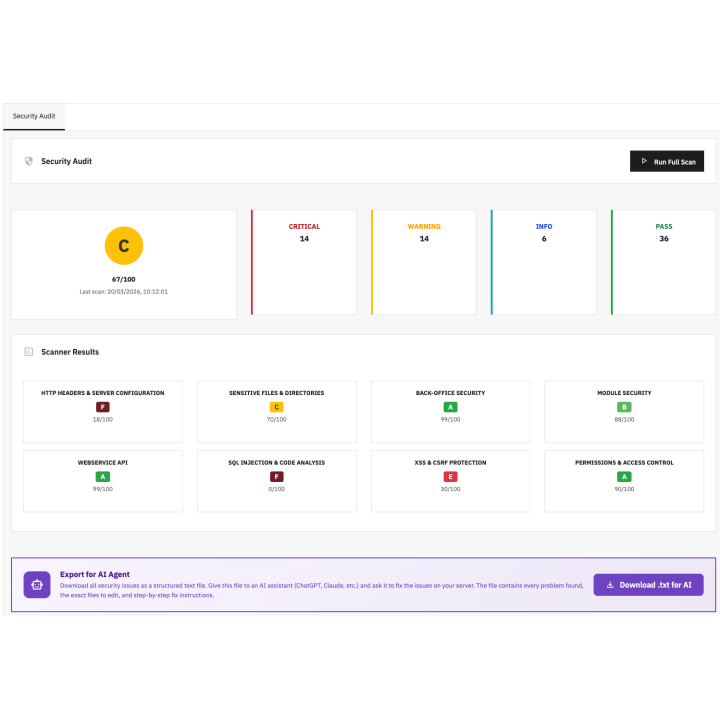
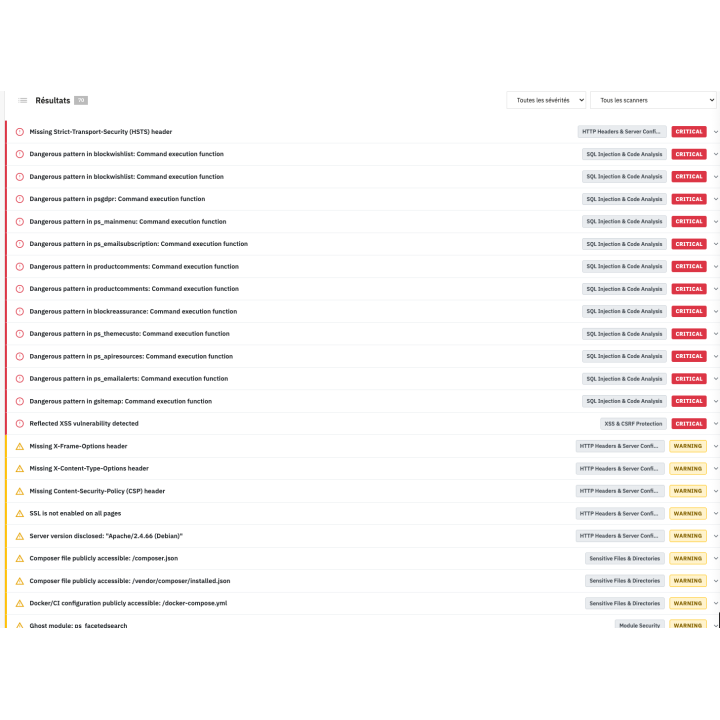
Step 2 — Review: Get your overall A-to-F security grade with a numeric score out of 100. Every finding is classified as Critical (red), Warning (orange), Info (blue), or Pass (green). Click on any finding to see the full explanation, fix steps, and technical details.
Step 3 — Fix: Either follow the step-by-step instructions provided for each finding, or click "Download .txt for AI" to export everything and let an AI assistant fix it all for you.
Export for AI Agent — The Game Changer
This is the feature that makes Security Audit Pro unique on the entire PrestaShop marketplace.
After scanning, click the "Download .txt for AI" button. The module generates a structured text file containing every detected problem, every file path to edit, and every fix instruction — formatted specifically for AI assistants to understand and act on.
Give this file to ChatGPT, Claude, Gemini, or any AI assistant and simply ask: "Fix every security issue in this report." The AI reads the structured report and patches each vulnerability, one by one.
The complete cycle:
- Detection — Security Audit Pro scans your store
- Diagnosis — Detailed report with plain-language explanations
- Export — Structured .txt file optimized for AI
- Fix — AI patches every vulnerability automatically
- Verify — Re-scan to confirm all issues are resolved
You no longer need to be a developer or hire a security consultant. The module finds the problems, explains them clearly, and your AI assistant fixes them.
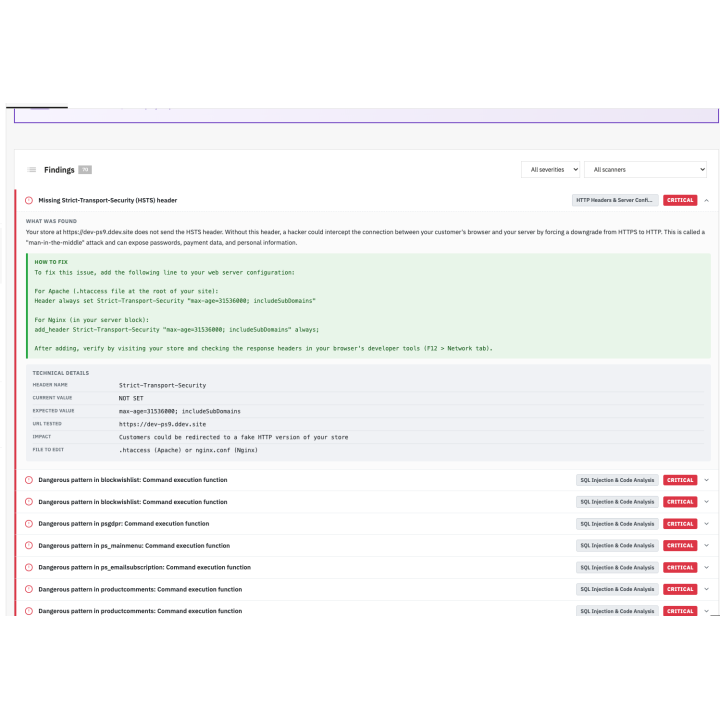
Detailed Finding Reports — No Expertise Required
Every detected issue opens into an expandable panel with three clearly separated sections:
WHAT WAS FOUND — A plain-language explanation of the problem. No jargon. The module tells you exactly what was detected, why it's dangerous, and what the concrete risk is for your store and your customers. Even someone with zero security knowledge can understand every finding.
HOW TO FIX — Numbered step-by-step instructions. Each step tells you exactly which file to open, what to look for, and what to change. No guessing, no Googling. Just follow the steps.
TECHNICAL DETAILS — For developers and advanced users: the exact file path, the detected pattern or code, the affected module or context, and the potential impact. This section is also what makes the AI export so effective — it gives the AI everything it needs to act.
Findings are organized in 8 tabs (one per scan category) and each one displays a color-coded severity badge (Critical, Warning, Info, Pass) and a category badge indicating which scanner detected it.
Section 1 — HTTP Headers & Server Configuration
Your server's HTTP headers are the first line of defense. Missing or misconfigured headers leave your store exposed to clickjacking, XSS attacks, MIME sniffing, and data leakage.
Security Audit Pro checks:
- 7 essential security headers: Strict-Transport-Security (HSTS), Content-Security-Policy (CSP), X-Frame-Options, X-Content-Type-Options, Referrer-Policy, Permissions-Policy, X-XSS-Protection — each one verified for presence AND correct value
- SSL/TLS certificate health: protocol version (TLS 1.2+ required), certificate expiration (alerts 30 days before), full chain verification, HTTP→HTTPS redirect (must be 301, not 302)
- Mixed content detection: scans your homepage HTML for resources loaded via http:// on an HTTPS page (images, scripts, stylesheets, iframes)
- Cookie security flags: Secure, HttpOnly, and SameSite attributes on every cookie, with priority focus on the PrestaShop session cookie
- Server information disclosure: detects if your server reveals its version (Apache/2.4.x, PHP/8.x), Symfony debug tokens (critical leak), or PrestaShop CMS identification
- CORS misconfiguration: tests if your server accepts cross-origin requests from any domain (wildcard), reflects malicious origins, or exposes credentials cross-domain
Section 2 — Sensitive Files & Directories
One of the most common and devastating attack vectors: files that should never be publicly accessible. A single exposed .env file can hand your entire database credentials to an attacker.
Security Audit Pro scans 40+ dangerous file paths:
- Configuration files: .env, .env.local, .env.backup, parameters.php, parameters.yml — contain database credentials, secret keys, SMTP passwords
- Debug files: phpinfo.php, info.php, test.php — reveal your complete server configuration to anyone
- Database tools: adminer.php, phpmyadmin/, pma/ — provide direct database access
- Version control: .git/HEAD, .git/config, .svn/entries — allow full source code reconstruction and credential extraction
- Composer files: composer.json, composer.lock — reveal all your dependencies and their versions
- Backup files: backup.sql, dump.sql, db.sql, backup.zip, backup.tar.gz — potentially contain your entire database in plain text
- CI/CD & IDE files: docker-compose.yml, .gitlab-ci.yml, .idea/, .vscode/ — may contain credentials and deployment configs
- Log files: var/logs/dev.log, var/logs/prod.log — may contain SQL queries, error traces, sensitive data
The module also detects directory listing on 10+ sensitive directories, verifies file permissions (CHMOD) on critical configuration files, and runs a full core file integrity check using SHA-256 checksums against official PrestaShop releases (1.7.8.x, 8.0.x, 8.1.x, 8.2.x, 9.0.x). Modified, deleted, or suspiciously added core files are immediately flagged.
Section 3 — Back-Office Security
Your back office is the ultimate target. If an attacker gets admin access, they own your entire store — customer data, orders, payment information, everything.
Security Audit Pro tests:
- Admin path strength: checks your admin directory name against 50+ common patterns used by automated scanners (admin, admin123, backoffice, bo, gestion, manage, backend, panel, etc.). If your path is guessable → Critical
- Brute force protection: simulates 5 rapid login attempts with fake credentials to test if your store has rate limiting, CAPTCHA, or IP blocking. No protection → Critical
- Two-factor authentication: checks if a 2FA/TOTP module is installed and active. 2FA is the single most effective protection against credential theft. Missing → Critical
- Admin accounts audit: scans for generic email addresses (admin@, test@, info@, root@), inactive accounts (not logged in for 6+ months), excessive SuperAdmin count (more than 2 = Warning, more than 5 = Critical), and disposable email domains (mailinator, yopmail, guerrillamail)
- Password policy: verifies minimum length enforcement and checks the actual hash format in your database — bcrypt ($2y$) is secure, 32-character MD5 hashes indicate dangerous legacy passwords that need immediate migration
Section 4 — Module Security
Third-party modules are the #1 source of vulnerabilities on PrestaShop stores. They represent over 80% of all exploited security flaws. This section is often the most eye-opening for merchants.
Security Audit Pro includes:
- Built-in CVE vulnerability database: every installed module is cross-referenced against a comprehensive database of known vulnerabilities sourced from Friends of Presta Security Advisories, TouchWeb advisories, and the National Vulnerability Database (NVD). If your module version is affected → Critical with CVE ID, vulnerability type, risk description, patched version, and advisory link
- Ghost module detection: finds modules that are disabled or uninstalled but whose files are still physically present on your server. These files remain accessible via direct URL — an attacker can exploit them even though you think the module is "removed"
- Obsolete module detection: identifies modules with declared compatibility lower than your PS version, or with PHP files unmodified for 2+ years (potentially abandoned by their developer)
- Unprotected endpoint scanning: checks for ajax.php, api.php, cron.php, callback.php, webhook.php, upload.php, export.php, download.php, proxy.php, connector.php, gateway.php files accessible without any authentication mechanism
- Upload handler analysis: performs static code analysis on every module's PHP files to detect file upload handlers (using $_FILES, move_uploaded_file) that lack MIME validation, extension whitelisting, or size controls. An uncontrolled upload → Critical (potential remote code execution)
Section 5 — WebService API Audit
PrestaShop's WebService API can expose your entire store data — customers, orders, products, employee accounts, configurations — via simple HTTP requests. A misconfigured API is a goldmine for attackers.
Security Audit Pro checks:
- API exposure: tests if /api/ responds without authentication (should return 401, not 200)
- Per-key permission audit: for each active API key, lists all authorized resources and methods. Flags: ALL resource access (Critical), DELETE on customers/orders/addresses (Warning), PUT/POST on configurations (Critical), access to employee data (Critical)
- Key strength analysis: evaluates each key's length (must be 32+), Shannon entropy (must be 3.5+ bits/char), and sequential pattern detection (123456, abcdef = weak)
- CORS on API endpoints: specifically tests /api/ paths for cross-origin misconfiguration — an active API with permissive CORS means any malicious website can read your store data from any visitor's browser
Section 6 — SQL Injection Detection & Code Analysis
SQL injection remains one of the most devastating attack types. A single vulnerable parameter can give an attacker access to your entire database — customer accounts, passwords, credit card tokens, order history.
Security Audit Pro combines dynamic testing with static analysis:
Dynamic testing (HTTP requests):
- Tests common PrestaShop GET parameters (id_product, id_category, id_cms, id_manufacturer, id_supplier, search parameter) with SQL error detection payloads
- Detects SQL error disclosure in HTTP responses (MySQL syntax errors, PDOException, SQLSTATE patterns)
- Tests NEVER go beyond error detection — no exploitation, no data extraction, no modification
Static code analysis (PHP source reading):
- Scans all PHP files in /override/ and /modules/ for dangerous patterns:
- Unsafe SQL queries: Db::getInstance()->execute() with direct concatenation instead of pSQL()/(int) binding
- Code execution: eval(), exec(), system(), passthru(), shell_exec(), proc_open()
- Obfuscated malware: base64_decode() followed by eval() — the classic backdoor signature
- File inclusion: include()/require() with $_GET/$_POST parameters (LFI/RFI)
- SSRF: file_get_contents() with user-controlled URLs
- PHP Object Injection: unserialize() with user data
- Deprecated dangerous functions: preg_replace() with /e flag
Results are grouped by module with an individual risk score, making it easy to identify which modules are the most dangerous.
Section 7 — XSS & CSRF Protection
Cross-Site Scripting (XSS) allows attackers to inject malicious scripts into your pages, stealing customer cookies, session tokens, and personal data. Cross-Site Request Forgery (CSRF) tricks authenticated users into performing unwanted actions.
Security Audit Pro tests:
- Reflected XSS: sends non-destructive payloads to your search bar, contact form, and URL parameters, then analyzes the HTML response to check if payloads are reflected without encoding. Unencoded reflection → Critical (exploitable XSS)
- CSRF token verification: checks every front-office form (contact, login, registration, address, checkout) and back-office form for the presence of anti-CSRF tokens (_token for Symfony, token for legacy PS)
- Content-Security-Policy evaluation: analyzes your CSP header specifically for XSS protection effectiveness — flags unsafe-inline, unsafe-eval, wildcards in script-src, and provides a recommended CSP configuration for PrestaShop
Section 8 — Permissions & Access Control
Security Audit Pro checks:
- PHP execution in upload directories: verifies that .htaccess rules block PHP execution in /upload/, /img/, /download/, /mails/. If an attacker can upload and execute a .php file → full server takeover
- Open redirect testing: tests redirect parameters (back, redirect, returnUrl, url, next, checkout) with external URLs and classic bypass techniques (//evil.com, /\evil.com). Open redirect → Critical (enables phishing attacks using your domain)
- IDOR protection: tests if orders, invoices, and addresses are accessible by simply incrementing the ID in the URL without authentication. Accessible → Critical
- Anti-bot protection: analyzes registration and login forms for CAPTCHA (reCAPTCHA, hCaptcha, Turnstile), honeypot fields, or rate limiting. No protection → Warning (exposes your store to mass registrations and credential stuffing)
Smart A→F Scoring System
The security score is calculated using a weighted formula where each scanner contributes according to its risk level:
- Back-Office Security: 20%
- Module Security: 20%
- Files & Directories: 15%
- HTTP Headers & Server: 10%
- WebService API: 10%
- SQL Injection & Code: 10%
- XSS & CSRF: 10%
- Permissions & Access: 5%
Each finding subtracts points based on severity: Critical = -30pts, Warning = -10pts, Info = -1pt. The score ranges from 0 to 100 and maps to a letter grade:
- A (90-100): Excellent — your store follows security best practices
- B (75-89): Good — minor improvements recommended
- C (60-74): Average — important corrections needed
- D (40-59): Insufficient — significant vulnerabilities detected
- E (20-39): Poor — serious risks, urgent action needed
- F (0-19): Critical — your store is vulnerable, act immediately
Dashboard, History & Comparison
The back-office dashboard gives you a complete overview at a glance:
- Large A-to-F grade with numeric score prominently displayed
- 4 severity counters: Critical / Warning / Info / Pass with color-coded icons
- 8 progress bars: one per scanner section with individual scores
- Scan history table: date, score, duration, PS version, PHP version, link to detailed results
- Scan comparison: when 2+ scans exist, see the trend — ↑ improvement (green) or ↓ regression (red) with exact point differential
- Real-time scanning: AJAX-powered progress bar showing which scanner is running and completion percentage
Track your security posture over time. Measure the impact of your fixes. Detect regressions after updates or new module installations.
100% Safe & Non-Intrusive
Security Audit Pro is designed to be completely safe to run on production stores:
- Read-only: the module never creates, modifies, or deletes any file on your server
- SQL injection tests: only detect error disclosure — zero exploitation, zero data extraction
- Brute force tests: limited to 5 attempts with intentionally fake credentials (test@test.com / wrongpassword123) and an identifiable User-Agent (WePresta-SecurityAudit/1.0)
- XSS payloads: non-destructive alert(1) only — no DOM modification, no data exfiltration
- Zero front-office impact: no hooks, no JavaScript, no CSS on your storefront. The module works exclusively in the back office
- Strict timeouts: 10-second timeout on every HTTP request to prevent slowdowns
Full Multistore Support
Each store in your multistore setup gets its own independent configuration, scan history, security score, finding reports, and AI export file. Scan each store separately and compare security levels across your entire network.
Modern Technical Architecture
- Dual controller system: Symfony controllers with Twig templates for PrestaShop 8.x and 9.x (Symfony 6.4), legacy ModuleAdminController with Smarty templates for PrestaShop 1.7.x
- Alpine.js dashboard: reactive, fast, modern back-office interface
- PSR-4 autoloading: clean, modular PHP architecture with 8 independent scanner classes implementing a common ScannerInterface
- Custom cURL wrapper: all HTTP requests use a dedicated HttpClient class with identifiable User-Agent, strict timeouts, and SSL verification
- Full translations: English (default) and French via .xlf files with the Modules.Weprestasecurityaudit.Admin domain
- No core overrides: zero modifications to PrestaShop core files
- Minimal requirements: cURL, JSON, and OpenSSL PHP extensions (standard on every hosting provider)
Who Is This Module For?
- Store owners who want to know if their store is secure — without needing any technical knowledge
- Agencies managing multiple PrestaShop stores who need a quick, repeatable security assessment tool
- Developers who want to audit their code and modules before deployment
- Anyone concerned about AI-powered attacks — because if you're not scanning your own store, someone else will
Why choose us?
See how we compare to the most common alternatives on the market.
| Feature | WePresta | Addons |
|---|---|---|
| payments Transparent pricing | check_circle | cancel |
| update Lifetime updates included | check_circle | cancel |
| support_agent Direct developer support | check_circle | cancel |
| verified PS 1.7, 8 & 9 compatible | check_circle | help_outline |
| code Standardized clean code | check_circle | cancel |
| storefront Multi-store ready | check_circle | help_outline |
| money_off No hidden renewal fees | check_circle | cancel |
Discover the module in images.
FAQ
Find answers to frequently asked questions about this module
Join +290 merchants using this module
5-minute installation · Full documentation included